
Routing can be contrasted with bridging in its assumption that network addresses are structured and that related addresses suggest proximity within the network. Structured addresses allow a single routing desk entry to characterize the path to a gaggle of units. In giant networks, the structured addressing utilized by routers outperforms unstructured addressing utilized by bridging. Unstructured MAC addresses are used for bridging on Ethernet and similar native space networks. The most putting instance of an overlay network is the Internet itself. The Internet itself was initially built as an overlay on the telephone network.
It might or is most likely not legal and will or may not require authorization from a court or other impartial agency. There are some ways to measure the performance of a network, as each network is different in nature and design. For instance, state transition diagrams are sometimes used to mannequin queuing performance in a circuit-switched network.
IP network delays can vary from a number of milliseconds to a quantity of hundred milliseconds. A nanoscale network has key parts carried out at the nanoscale, including message carriers, and leverages bodily rules that differ from macroscale communication mechanisms. ATM still performs a task in the last mile, which is the connection between an Internet service supplier and the home consumer. Bridges and switches divide the network’s collision domain however preserve a single broadcast area. Network segmentation via bridging and switching helps break down a large, congested network into an aggregation of smaller, more environment friendly networks.
Network Service
The administrative entity limits the utilization of the intranet to its approved customers. Most generally, an intranet is the internal LAN of an organization. A massive intranet sometimes has no less than one internet server to supply users with organizational information. A campus space network is made up of an interconnection of LANs within a limited geographical space. The networking gear and transmission media (optical fiber, Cat5 cabling, and so on.) are nearly entirely owned by the campus tenant or owner (an enterprise, university, government, and so on.).
For instance, an organization might present access to some features of its intranet to share information with its enterprise companions or clients. These different entities aren’t necessarily trusted from a security standpoint. The network connection to an extranet is usually, but not all the time, applied via WAN technology. An intranet is a set of networks which are underneath the control of a single administrative entity. An intranet usually uses the Internet Protocol and IP-based instruments such as internet browsers and file switch purposes.
It presents connection-less and connection-oriented companies over an inherently unreliable network traversed by datagram transmission using Internet protocol . The Internet protocol suite is the defining set of protocols for the Internet. FirewallsA firewall is a network gadget or software for controlling network safety and entry guidelines. Firewalls are inserted in connections between safe inside networks and potentially insecure external networks such as the Internet. Firewalls are sometimes configured to reject entry requests from unrecognized sources whereas permitting actions from acknowledged ones.
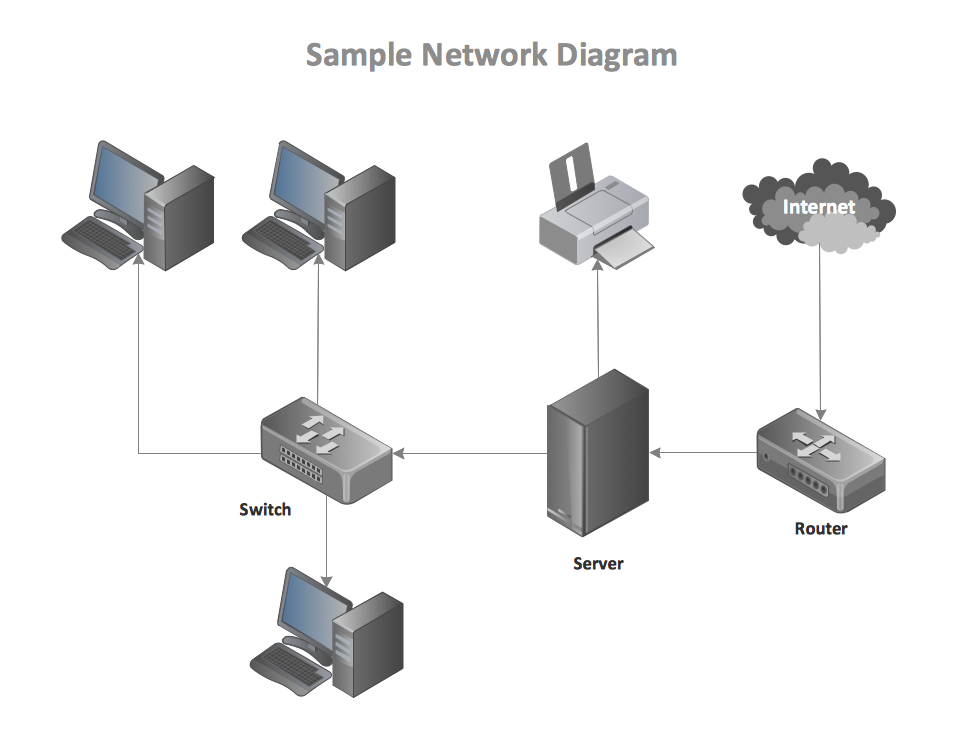
Computer network structure defines the physical and logical framework of a computer network. It outlines how computers are organized within the network and what tasks are assigned to these computers. Network architecture elements include hardware, software program, transmission media , network topology, and communications protocols.
Metropolitan Space Network
Computer network, two or more computers which would possibly be connected with each other for the purpose of speaking knowledge electronically. Two well-liked architectures are ISO Open Systems Interconnection and IBM’s Systems Network Architecture . Before the advent of recent networks, communication between totally different computer systems and units was very complicated. Mechanical switches have been used so that peripheral units is also shared. Due to bodily limitations , the units and computer systems always needed to be very close to each other.
The network planner makes use of these diagrams to investigate how the network performs in each state, guaranteeing that the network is optimally designed. A certain minimal level of delay is experienced by indicators because of the time it takes to transmit a packet serially via a hyperlink. This delay is extended by extra variable ranges of delay because of network congestion.
It Asset Management Software
IPv4 addresses was standard, however solely a complete of around 4.3 billion of these addresses could possibly be assigned earlier than they were exhausted. Due to the huge expansion of the Internet, further IP addresses were urgently needed. Therefore, the new IPv6 normal was developed, permitting up to three.4 x addresses. Network resilience is “the power to offer and preserve a suitable degree of service within the face of faults and challenges to normal operation.”
A pc network is a set of computer systems sharing sources positioned on or provided by network nodes. Computers use widespread communication protocols over digital interconnections to communicate with each other. These interconnections are made up of telecommunication network technologies based on physically wired, optical, and wi-fi radio-frequency methods which could be organized in a variety of network topologies. In packet-switched networks, routing protocols direct packet forwarding through intermediate nodes. Intermediate nodes are typically network hardware units similar to routers, bridges, gateways, firewalls, or switches. General-purpose computer systems also can ahead packets and perform routing, although as a result of they lack specialized hardware, could offer limited performance.
